What Is app-ads.txt and How Does It Work?
Ad fraud remains one of the most persistent and costly threats to programmatic advertising. Industry research by cybersecurity company CHEQ estimated that fraudulent activity against digital advertising cost the industry $35 billion globally in 2020. Other analyses place that figure somewhere between $6.5 billion and $19 billion. Regardless of which estimate you trust, the financial damage is substantial across the entire digital advertising ecosystem.
A range of companies — including CHEQ, DoubleVerify, WhiteOps, Pixalate, and Fraudlogix — have built dedicated fraud detection and prevention tools in response. On the standards side, the IAB Tech Lab has introduced mechanisms like ads.txt to help address specific fraud vectors — namely domain spoofing and illegitimate inventory arbitrage — by allowing publishers to publicly declare which companies are authorized to sell their inventory.
The logic is straightforward: if an SSP or ad exchange appears in a buyer's RTB request and also appears in the publisher's ads.txt file, that seller is authorized. If there's no match, the seller may be unauthorized or fraudulent.
Ads.txt, however, was designed for web browser environments. Domain spoofing and illegitimate arbitrage are equally prevalent in mobile in-app and over-the-top (OTT) environments — and that's the gap app-ads.txt was built to close.
What Is app-ads.txt?
Released on March 13, 2019, app-ads.txt is an extension of the Authorized Digital Sellers (ads.txt) standard, developed by the IAB Tech Lab specifically for in-app and OTT environments. Its primary purpose is to combat domain spoofing and reduce opaque practices like inventory arbitrage in mobile and connected TV contexts.
How Does app-ads.txt Work?
App-ads.txt follows the same core logic as ads.txt, with a few important differences in how the file is discovered and retrieved.
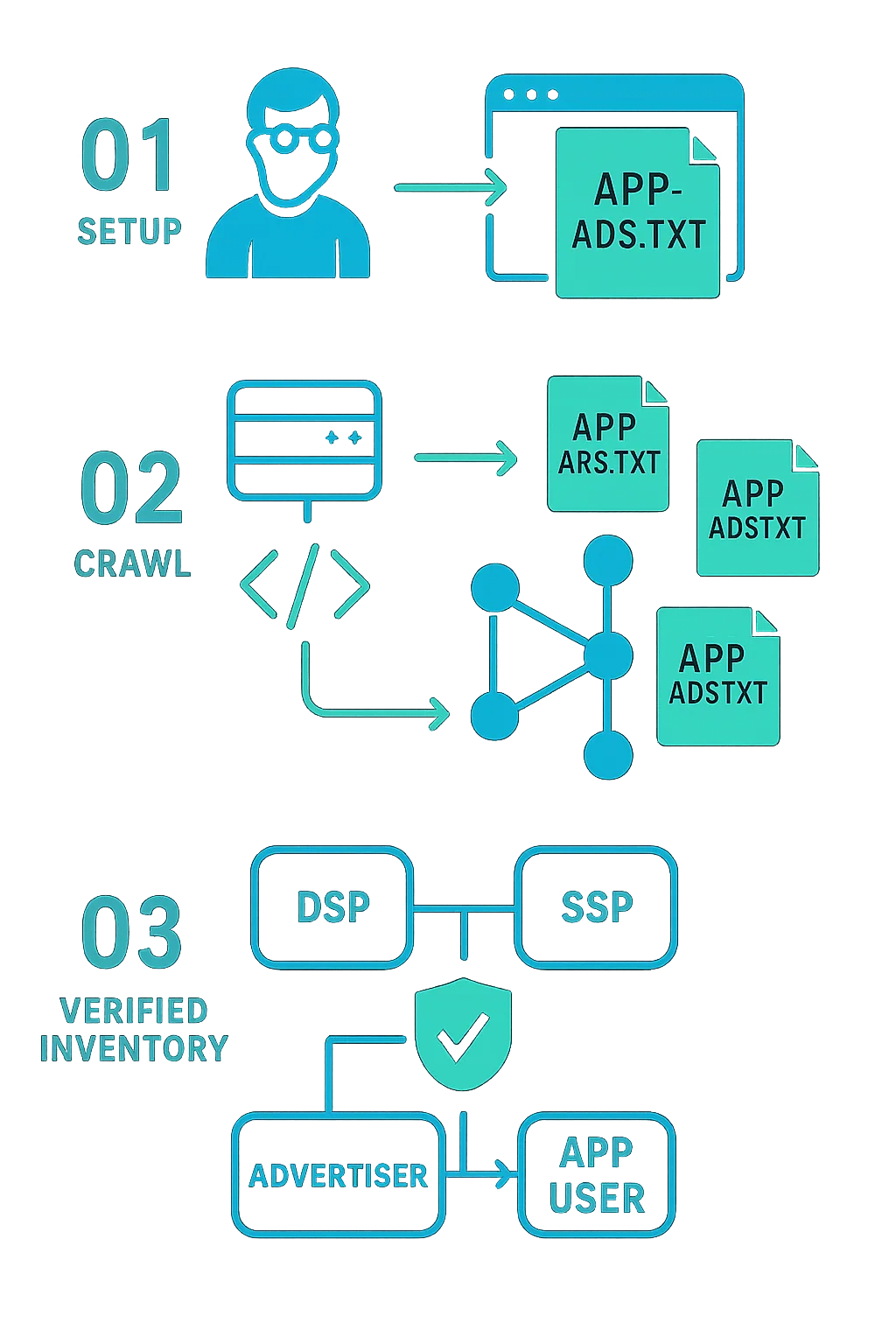
Mobile and OTT app developers create an app-ads.txt file on their developer website that lists every AdTech vendor authorized to sell or resell their ad inventory. They then link to that developer website within their app store listing metadata:
<meta name="appstore:developer_url" content="https://www.app-dev1.com" />
From there, media buyers — including advertisers and DSPs — crawl a database of app developer websites, translate those URLs into app-ads.txt file paths, and retrieve the files. DSPs can then cross-reference the app-ads.txt entries against the information contained in RTB bid requests to verify whether a given SSP or ad exchange is actually authorized to sell that app's inventory.
What's Inside an app-ads.txt File?
Each entry in an app-ads.txt file contains up to four fields:
- SSP/AdTech platform name — The platform the publisher uses to sell inventory (e.g. pubmatic.com, magnite.com).
- Seller Account ID — The publisher's account ID with that AdTech vendor. This is used to verify inventory authenticity during RTB auctions.
- DIRECT or RESELLER — Indicates whether the publisher works directly with the vendor (
DIRECT) or has authorized a third party such as an ad network to sell on its behalf (RESELLER). - Certification Authority ID (optional) — Identifies the advertising system within a certification authority, such as the Trustworthy Accountability Group (TAG). An example value would look like
g45tg4e.
What Problems Does app-ads.txt Solve?
App-ads.txt targets two specific fraud mechanisms common in mobile and OTT environments.
Domain spoofing is a technique where fraudsters manipulate RTB signals to make DSPs believe they are bidding on inventory from premium, brand-safe apps. In reality, the impressions come from low-quality or dummy apps created solely for fraud. Domain spoofing is frequently used to monetize apps that would otherwise be blacklisted or ignored by advertisers.
Inventory arbitrage refers to the practice of buying impressions, repackaging them, and reselling them to buyers at a higher price — often without the original publisher's knowledge or consent. App-ads.txt makes unauthorized reselling visible by requiring that any reseller be explicitly listed in the publisher's file.
Adoption of app-ads.txt
As with most programmatic advertising standards, the practical value of app-ads.txt depends heavily on how widely it is adopted across the ecosystem.
Early signs were encouraging. Fraud detection firm Pixalate found that app-ads.txt usage grew 177% between Q1 and Q2 of 2019, then surged to 1,222% growth in Q3 2019, reaching 111,875 implementations by the end of November 2019.
According to IAB Tech Lab data, more than 25,310 iOS apps and over 86,565 apps in Google Play had enforced app-ads.txt files during that period. MoPub reported an 82% adoption rate among its managed app publishers.
The clearest driver of broader adoption is likely buy-side enforcement. As reported by AdExchanger, DSPs including Centro, Google's DV360, and The Trade Desk have begun requiring app-ads.txt compliance. When DSPs stop purchasing inventory from publishers who haven't implemented the standard, the revenue risk becomes a strong incentive for publishers to get on board. Enforcement from the buy side, more than any industry initiative on its own, is what tends to accelerate adoption of these kinds of standards.